The following are the CSPC 2020 panels that cover
Challenges in a Digital Age
Pre – Conference Day 8 – November 12th 2020
Organized by: Ryerson University
Panel One: Playing Well With Others: Approaches to Cybersecurity Collaboration in Canada
Dr. Mourad Debbabi – Professor, Concordia Institute for Information Systems Engineering, Concordia University
Dr. Ali Ghorbani – Professor, Faculty of Computer Science, University of New Brunswick
Dr. Florian Kirshbaum – Professor, School of Computer Science, University of Waterloo
Dr. Emily Laidlaw – Associate Professor, Faculty of Law, University of Calgary
Dr. Atty Mashatan – Assistant Professor, Ted Rogers School of Information Technology Management, Ryerson University
Charles Finlay – Executive Director of Rogers Cybersecure Catalyst
Context: The panel discussed how industry, academic institutions and governments can effectively collaborate to meet the challenges of cybersecurity in Canada, and how roadblocks to effective collaboration can be overcome. An example of such a model is the new National Cybersecurity Consortium.
Takeaways:
- Barriers to collaborative success in Canada include: “turf” and siloed mentalities; determining which level of government to engage (privacy and security have no borders), finding the right industry partner (to ensure that the partner can bring innovations to scale).
- Successful collaborations depend on knowledge sharing between experts in different sectors, including industry and academia, and from different fields (e.g, law, technical, business)
- Key is the need to innovate; new product beyond typical code – key to keeping academia-industry relationships alive
- Governments have changing mandates. It is important for industry and academic partners to keep this in mind when considering accountability and scope.
- A potential collaborative model is a civic society approach (e.g., UK model currently in development). This would encompass not-for-profit groups that can provide oversight across different sectors with a goal of breaking silos. Different NFPs would be necessary to advocate for specific issues within the cybersecurity umbrella (e.g., technology rights).
Actions:
- All relevant sectors and groups must join forces and consider cybersecurity issues as a multidisciplinary grand challenge.
- Consider the business model and mandate of stakeholders in each sector. For example, academics cannot view industry partners as financial contributors only, and industry cannot view academic or federal partners as only vendors.
- Cybersecurity grand challenge goals and themes should come from a consensus-based approach to ensure alignment with all stakeholders at the table. This will ensure it is feasible, and that priorities are set.
–
Panel Two: Tackling the Labour Market Shortage in Cybersecurity
Kathy Knight – Executive Director, Cyber Security Technical Centre of Excellence, Manitoba Institute of Technology
Angela Mondou – President and CEO, Technation
Max Shuftan – SANS Institute
Rushmi Hasham – Director of Training, Rogers Cybersecure Catalyst
Context: The panel showcased training and industry experts in a conversation about the acute shortage of skilled cybersecurity talent in Canada and globally, and how this challenge is being met through new and innovative programs.
Takeaways:
- Cybersecurity is a fast growing sector in need of highly qualified personnel at all levels. Many companies are responding internally by training individuals with diverse educational backgrounds that can incorporate some aspects of cybersecurity (e.g., supply chain security analyst, security-automation engineers, AI and risk for cybersecurity).
- There are no standards for training in the cybersecurity sector. Training varies in complexity and consistency.
- Though there is a known talent shortage, the exact number and type of needed talent is unknown. This makes identifying training needs and informing policy difficult.
- Career-pathways are not clear and cybersecurity requires a diverse set of skills.
- Featured models to increase the development pipeline include:
- Grade 11 & 12 curriculum model at the 3rd year computer science degree program at the University of Manitoba. The student earns a full year credits toward undergraduate degree in Cyber Defense and Cloud Administration at MITT. [D1]
- Manitoba Institute of Trades and Technology: A program with stackable microcredentials tailored for all individuals interested in a specialization for in-demand jobs.
- SANS Immersion Academy: An accelerated training program that provides SANS training and Global Information Assurance Certification (GIAC) to quickly launch careers in cybersecurity. The Academies are 100% scholarship-based and free to participants.
- Rogers Cybersecure Catalyst cybersecurity program at Ryerson, in collaboration with SANS Immersion Academy program.
- TechNation is making progress on several challenges: launched cybersecurity skills framework; developed 22 national occupational standards around core cybersecurity roles; developed a career-ready platform and job availability “heat map” showing real time labour market data.
- Protectionism (e.g., union/employer considerations) is still a hurdle to integrated learning
Actions:
- Develop stimulation and operational training that allows for cybersecurity real-time training.
- Create pathways that lead to increased engagement of women and BIOPC (black, indigenous, people of colour) individuals
- All companies should incorporate some aspect of work-integrated learning so students can learn on the job, and allow sabbaticals so employees can take courses (e.g., micro credentialing).
Conference Day 2– November 17th 2020
Organized by: Canadian Statistical Sciences Institute
Panelists:
Amanda Edmunds – Director, Privacy Act Compliance, Office of the Privacy Commissioner of Canada (OPC)
Anne-Sophie Charest – Associate Professor, Department of Mathematics and Statistics, Université Laval
Donald J Estep – Director, Canadian Statistical Sciences Institute
Erin Rancourt – Director General, Modern Statistical Methods and Data Science Branch, Statistics Canada
John M Abowd – Associate Director for Research & Methodology and Chief Scientist, United States Census Bureau
Tanya Brown – Associate Director for Research & Methodology and Chief Scientist, United States Census Bureau
Context: Accurate and timely official statistics are needed by businesses, governments, and all Canadians to make informed decisions and the development of sound economic and social policies. The challenge lies in finding a balance between obtaining the necessary information for these accurate and timely statistics and the privacy of individuals and organizations. In a world where data is now the most important resource, how can national statistical organizations produce the accurate and timely information being requested but still ensuring the confidentiality of the data and the non-invasiveness of data collection?
Takeaways:
- In discussing privacy protection, we must consider three dimensions: the right to not disclose information about oneself; the right to control how one’s information is used; and the right to be left alone.
- Accurate and timely official statistics are needed by businesses, governments, and all Canadians to make informed decisions and the development of sound economic and social policies.
- There are challenges associated with finding a balance between obtaining the necessary information for accurate and timely statistics and the privacy of individuals and organizations.
- It is important that the activities underlying official statistics are trusted by the public and that there are laws to protect public privacy. However, confidentiality protection is often enshrined in legislation that does not recognize the trade-off between statistical precision and privacy loss.
Actions:
- Senior decision-makers in government agencies should be able to interpret privacy laws and deliver statistics that meaningfully address data use cases while protecting the confidentiality of the public.
- To reflect nuances in privacy, more legislation that recognizes the trade-off between statistical precision and privacy loss has to be developed. In the US, the Census Act (last modified over 20 years ago) states that the government has to protect confidentiality. However, the methods that statistical agencies have used to protect confidentiality are vulnerable to modern data science techniques.
- More research is needed on how to mathematically measure privacy and understand how individuals define privacy. Statistics Canada is gathering information on data sensitivity and coordinating focus groups to understand more about data privacy and sensitivity. It will also be important to build fairness and equity into official statistical models.
- Necessity and proportionality are needed in maintaining a balance between social good/benefit and individual rights to privacy. Government agencies have to make sure that privacy laws are proportional to the social benefit gain of official statistical methods.
Conference Day 3 – November 18th 2020
Organized by: Natural Resources Canada
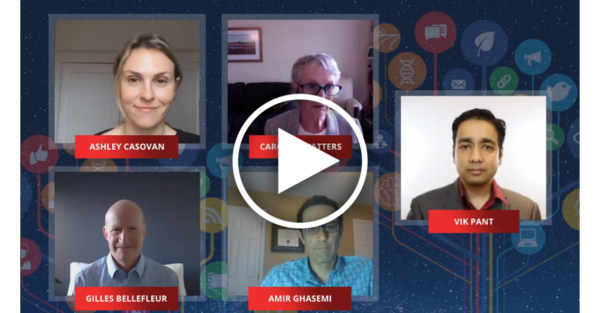
Panelists:
Vik Pant – Chief Scientist, Natural Resources Canada
Giles Bellefleur – Senior Research Scientist, Natural Resources Canada
Carolyn Watters – Chief Digital Research Officer, National Research Council
Ashley Casovan – Executive Director, Al Global
Amir Ghasemi – Research Scientist, Innovation, Science and Economic Development Canada, Communications Research Centre Canada (CRC)
Takeaways:
- Artificial Intelligence is here to stay, forcing policymakers to ask ‘when and how quickly will it be implemented’, rather than ‘if it will be implemented’. As research questions become more complex, it is no longer viable to do science at scale without some kind of machine learning or use of AI.
- Public expectations about connectivity, timeliness, availability of information, and the value-added of computing are not aligned with Canada’s current federal data practices. While the government has access to large quantities of data, the data is often underutilized because it unorganized or stuck within a repository.
- Leadership is crucial to the successful implementation of AI. Top-down prioritization of AI will allow ideas to translate into practice, allowing working-level individuals to adopt new paradigms and focus on new areas of study.
- AI is not a silver bullet for all of society’s issues. It remains a highly experimental field, where off-the-shelf solutions are unlikely to fit the needs of each individual department. As such, datasets need to be adapted to suit specific purposes.
- To ensure that AI is responsible and unbiased, ethical principles need to be encoded into all stages of a product’s design, development and release, as well as in post-release system reviews and software updates. The design should reflect core government values (e.g., minimizing costs or building a more equitable system?).
- Canada’s proposed new privacy bill makes significant progress in approach to data systems, but fails to address concerns related to the relationship between data and discrimination.
Actions:
- Policymakers should be in frequent contact with their technology development counterparts to ensure that they are in line with current and anticipated technology developments. This will ensure that policies are designed to address anticipated issues as well as current ones, thereby ensuring that they hold up in the long term.
- The federal government must level the playing field to ensure that all Canadians have access to new technologies. The federal government should also ensure that there is fairness in the distribution of the benefits of these technologies so that they are not limited to a small number of monopolies.
- The federal government must ensure there is diverse representation in AI system design, among those developing the systems and those populations for which the systems are created.
- There is a need to improve data infrastructure so that data can be better shared between departments and agencies. As no single approach will accurately address the needs of every department and its security standards, customization will be required.
- The federal government must ensure that there is accountability within AI-enabled systems. Canada needs a more complete suite of standards in terms of acceptability, accuracy, and explainability in these systems. This could be done through a certification mark, which would ensure that applicable standards are implemented properly.
Conference Day 1 – November 16th 2020
Organized by: ISED
Panelists:
Joy Johnson – President and Vice Chancellor, Simon Fraser University
Martha Crago – Vice Principal, McGill University
Eric Bisaillon – Director, Security Architecture Branch, Canadian Centre for Cyber Security (CCCS)
Tricia Geddes – Deputy Director, Policy & Strategic Partnerships, Canadian Security Intelligence Service
Context: Research security and globalized events like the COVID-19 pandemic continue to influence the threat landscape. Canada’s strong science and research ecosystem makes it an attractive target for malicious actors who want to acquire knowledge, research, and intellectual property to advance their own initiatives. Panelists discussed how Canada can safeguard research and mitigate potential risks, while maintaining a commitment to open and collaborative science.
Takeaways:
- There are shifting security threats targeting Canadian science, research and innovation that are dramatically changing the way Canadian security agencies such as the Canadian Security Intelligence Service (CSIS) and the Canadian Centre for Cyber Security (CCCS) engage with the public and institutions outside of government.
- The mandates of the intelligence agencies are no longer limited to government, but now include academia and business, which are increasingly being targeted by hostile state actors seeking to steal or undermine Canadian research, science, intellectual property, technology and expertise.
- The Canadian government’s response to COVID-19 with massive funding of research for a vaccine exposed a significant increase in targeting of Canadian R&D by hostile foreign actors.
- CSIS’ new branch, Academic Outreach and Stakeholder Engagement, took unprecedented action to increase the awareness and understanding of higher education and research-based businesses on security threats and to provide guidance on mitigation. At the same time, they worked closely with other GoC partners to establish the secure networks needed to acquire a timely and effective vaccine.
- Academia is struggling to accept the reality of insidious threats by hostile actors. One reason is because the threats with global research partnerships are not always obvious and collaborations are taking on new forms that don’t involve funding or formal MOUs, such as co-authorships and data sharing. This makes it difficult to track and monitor, and raises new concerns such as ethical implications of these less formal collaborations.
- Researchers struggle to understand the reality and implications of the threats when long-time partnerships/collaborations are now associated with questionable organizations or when security clearances restrict the information that can be shared to ‘prove’ the existence of a threat or fully grasp the covert strategies used by hostile state actors.
- Our relationship with the Five Eyes is unaffected by surface-level geopolitical issues and is one of our principle tools in our toolbox. The excellent collaboration and intelligence sharing between the Five Eyes is of great benefit to Canada and likely causes our adversaries to stay up at night.
Actions:
- New and innovative partnerships between higher education and security intelligence agencies need to work collaboratively to mitigate threats.
- Consider new forms of security clearance to allow briefing ‘intermediaries’ who bridge the divide between security intelligence experts and researchers.
- While continuing to address the issue of foreign actors targeting Canadian R&D, we must work to prevent scapegoating and prejudice against innocent individuals and communities.
Conference Day 1 – November 16th 2020
Organized by: Concordia University
Panelists:
Mourad Debbabi – Professor, Concordia Institute for Information Systems Engineering, Concordia Institute
Marthe Kassouf – Researcher, Hydro Quebec Research Institute (IREQ)
Deepa Kundur – Professor & Chair, Edward S. Rogers Sr. Department of Electrical & Computer Engineering, University of Toronto
Benoît Dupont – Professor of Criminology, Université de Montréal
Martin Fontaine – Chief Research Officer, CSE
Context: National Critical Infrastructure (NCI) encompasses an array of systems and sectors essential for the health, safety, economic activity and function of Canadians, but with each sector embracing digitalization and automation, exposure to large-scale cyber-attacks has increased at an alarming pace. Protecting NCI is a significant challenge, given the enormous footprint and complexity of its systems, facilities and networks (e.g., power grids, telcos, and transport networks). This panel discussed the grand challenges of protecting NCI systems and explored solutions based on: (a) enhanced collaboration and information-sharing catalyzed by increased levels of trust; (b) the mutual benefits stemming from collaborative undertakings; and (c) access to better funding and R&D opportunities.
Takeaways:
- It’s of paramount and strategic importance to invest in NCI. It constitutes about 58.1% of Canada’s GDP, or $1 trillion in goods and services and involves 380,000 companies, of which 1,500 are large organizations.
- One of the most significant challenges is Canada’s personnel gap in cybersecurity. We need to fill an estimated 8,000 additional cybersecurity positions by 2021.
- Many sectors use legacy equipment that relies on outdated architectures, and there are abundant, hard-to-fix security flaws within these highly connected environments which makes them vulnerable to cascading effects (such as blackouts) following an attack.
- Cyberinfrastructure sectors are converging. The telecommunications sector, in particular, connects everyone to their digital assets, and we need a robust system in place to trust in these interconnections.
Actions:
- The sophistication level of explaining a situation and how to defend and mitigate varies across sectors. We need to develop a tool box that tailors services and recommendations to the maturity level of the sector.
- Embed academia in private or public organizations and cybersecurity officials into academia to develop trust and build partnerships through hubs, secondments and placements. Train students to understand that silos are breaking down and to value transdisciplinary experiences.
- Invest in technical skills, emergency training and in understanding how humans in cyberinfrastructure systems can work together to address security risks. More research is needed to understand the psychological state of the people when handling cyberinfrastructure systems and training them in how to react.
- Canada is lagging in developing a national plan that includes public and private sector organizations as well as academia. The plan needs to include a baseline of regulations for cyberinfrastructure systems and should embrace a “whole-of-government” regulatory approach.
- Set up information hubs and automation channels to facilitate the exchange of information about best practices and intelligence between sectors in real time.
- Embrace that information technology/operational technology convergence exists and that we are in a “big data” scenario. Automation and digitalization increases our attack surface so we must be able to predict system vulnerabilities and develop a robust, integrative system.
Conference Day 4– November 20th 2020
Organized by: Journal of Science Policy & Governance
Panelists:
Saheel Mehta – Director of Communications, Journal of Science Policy & Governance